While the first arms race took place at the atomic level, the next arms race may take place at an even smaller scale: the quantum level. The 20th century brought about groundbreaking discoveries of how particles act on very small scales, which have inspired many inventions, most of which have not been realized yet. Just like the nuclear revolution, the possible ramifications of the quantum revolution reach far beyond the spheres of academia and may become instrumental in security and warfare. For example, quantum computing has been the dream (and nightmare) of researchers, cybersecurity experts, and intelligence agencies alike, with the promise of processing speeds far above those of any existing computer and the ability to break traditional encryption methods. Strange quantum properties like “entanglement” could lead to the advancement of radar and compass technologies. While current quantum technology is still short of these capabilities, these alluring promises have motivated countries across the world to invest in quantum research, each hoping to be the first to gain the advantage of quantum-powered cybersecurity and defense.
What is Quantum Technology?
Quantum technology covers a large range of technology that uses subatomic particles and their quantum mechanical properties. The most common subatomic particles encountered in quantum technology are electrons and photons. Electrons are very small particles that orbit around the center of atoms, and photons are essentially particles of light. These particles can act in counterintuitive ways, one of which is that they can be in multiple states at the same time, a property called superposition. While the actual names of these quantum states is unimportant in this article, the key thing to note is that these particles can hold contradictory information—i.e., a particle can be “yes” and “no” at the same time. Another strange property of subatomic particles is quantum entanglement, or as Einstein dubbed it, “spooky action at a distance.” In a nutshell, entanglement is a linking between two particles, where the state of one particle has an influence on the state of the other particle.
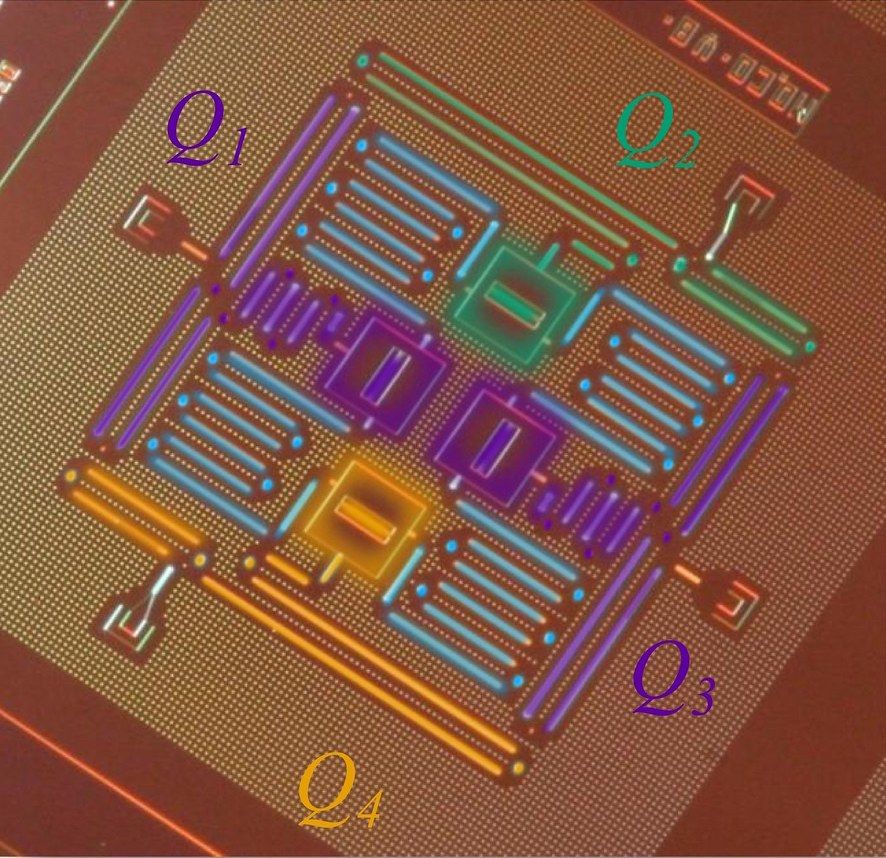
One of the most famous applications of quantum technology is in computing. In traditional computers, information is represented through bits, which are electrical or optical pulses that can take the value of 1 or 0 (1 = on, 0 = off). In quantum computers, the “qubits” are not pulses but subatomic particles like electrons or photons. Because of superposition, each qubit can represent multiple values at once, so the computer can evaluate multiple calculations at the same time, rather than sequentially like a traditional computer would. Thus, quantum computing has the potential to overwhelm traditional computers thanks to the much higher computational speeds it offers. This is especially apparent with very large calculations, with some examples being factoring very large numbers (often used in cybersecurity, which will be examined later) and mapping the shortest path between two points. In these examples, the quantum computer has an advantage because it can simultaneously consider every combination of numbers or paths, while a traditional computer would have to crunch through every possible path separately.
Weapons and Defense
With current radar technology, radio waves are sent out from a transmitter, and if they hit an object, they are reflected back. These reflected waves can be detected by a receiver, and thus the location of the object can be calculated. However, modern stealth planes like the Northrop Grumman B2 Spirit use features like metal-coated windows, zig-zag wing designs, concealed exhaust pipes, and rounded front wings to absorb or scatter radio waves, making the waves that reflect back to the receiver indistinguishable from background noise.

Quantum radar is designed to be a level up from conventional radar: it uses properties of quantum entanglement to beat radar jamming methods used in stealth planes like the B2 stealth bomber. The concept of quantum radar originates from Seth Lloyd, a quantum engineer at MIT, who theorized that one can entangle two photons, transmit one of the two out to an object, and then look for the reflected photon through the receiver. Since one photon in the entangled pair remains at the transmitter, its state can be measured, and so the state of the other photon is also known. The receiver can then look for these correlated states (essentially entanglement “signatures”) in the reflected waves, which can more accurately differentiate target signals from background noise.
However, the current technologies developed in the United States are nowhere near this dream of invincible radar detection. Many technical difficulties still stand between making quantum radar viable for practical purposes, such as the need to keep entanglement generators at temperatures near absolute zero. Even with these difficulties and skepticism within the quantum research community, reports of successful prototypes of quantum radar from the China Electronics Technology Group Corporation (CETC), one of China’s most prominent defense technology companies, has spurred a surge in US interest in quantum radar. Many American quantum researchers are skeptical of these claims, yet the threat of falling behind China militarily has kept quantum radar on the US military agenda. While US stealth technology is one of the best in the world, the success of quantum radar could signal the end of the US stealth dominance.
Cybersecurity
To national security experts, what may be more troubling than quantum radar is the use of quantum technology in encryption and cybersecurity. The general process of data encryption is through the use of a generated “key”, which is used to scramble content sent over the internet. Then, once the data reaches its intended destination, the content is unscrambled using that key. There are different systems of encryption as well as different algorithms to create the key, with varying levels of security. However, many advanced computational systems can crack these keys, especially those used for less secure information, like the data we send in an iMessage or WhatsApp call. As computers get faster and algorithms become more advanced, the two effects compete, so cybersecurity measures must be constantly updated.
This is where quantum technology can provide a massive advantage. Quantum keys are encoded into the states of subatomic particles. Since the states are determined by observation, if a hacker manages to view the key, they will leave traces of observation in the states of the particles. Therefore, the receiver will be able to tell that the key is not secure, and another key can be generated. This method of encryption is called quantum key distribution (QKD). In addition, ideal quantum computers could perform intensive computations like Shor’s algorithm (calculating prime factors of very large numbers), which is often a component of creating an encryption key. While conventional computers are quickly bogged down when presented with larger numbers, quantum computers can compute very large numbers quickly and efficiently, making keys that are much more secure. On the side of the hacker, quantum computers can crack traditional and sometimes even quantum encryption keys by attempting many computations or guesses simultaneously. According to the latest Thales Data Threat Report, “72 percent of [surveyed] organizations see it affecting their cryptographic operations in the next five years” and “ninety-two percent of respondents are concerned quantum computing will create exposure for sensitive data.” Essentially, quantum computing is a double-edged sword for the cybersecurity industry: it can make both creating keys and breaking them easier.
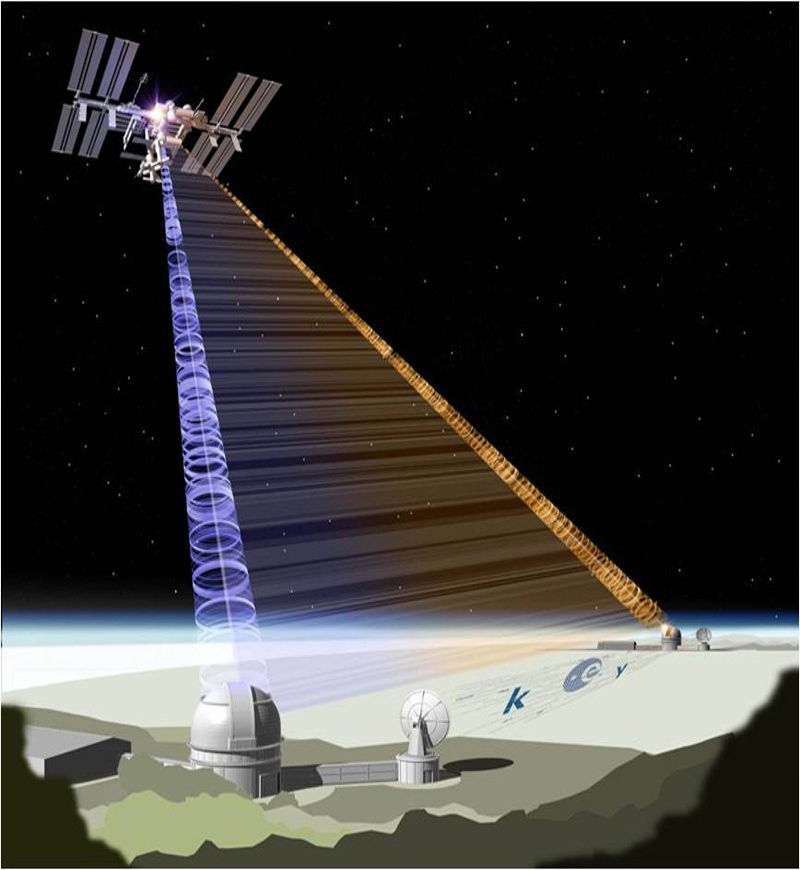
So far, researchers at the University of Science and Technology in China (USTC) have succeeded in sending quantum keys between Chinese satellites and ground stations, as well as quantum communications between cities in China, signaling a new milestone in wireless quantum communications. In the United States, researchers are developing something called “quantum teleportation,” which uses entanglement to transfer data between sending and receiving qubits, creating a one-time secure data transfer link. None of these technologies are completely secure or reliable yet, so, for now, traditional key encryption is still the most widely used cryptography technique, and traditional encryption algorithms are being developed to combat possible quantum attacks in the future. Even with technical setbacks, the competition to develop a secure quantum security system is tight, since each country wants to claim the military and security advantage.
International Initiatives
Historically, the United States has been reluctant to invest in the uncertain arena of quantum technology, but China’s rapid developments in recent years have spurred the United States into action. China has offered almost unlimited funding to quantum researchers, investing US$10 billion in one quantum laboratory alone. In 2017, US Congress passed the National Quantum Initiative Act, establishing programs and incentives for quantum information technology, as well as a committee to advise the President on quantum developments. In February 2020, the Trump administration announced a US$1 billion investment in quantum computing and related fields. This occurred in the context of China’s surge in quantum communications patents, as the country’s yearly patents have outnumbered the United States in every year since 2012 and has shot up to over 500 new patents in 2018 alone (compared to the United States’ 117). Outside of the United States and China, the European Union is investing US$1.1 billion over 10 years in its Quantum Flagship project, while the United Kingdom plans to spend US$400 million developing quantum sensors. Canada, Australia, and Israel also have national efforts behind quantum research.
While US government expenditures on quantum initiatives are coming much later in the game than other countries, the US private sector has remained extremely competitive in terms of quantum technology. Google and IBM have competed fiercely to build quantum computers that can outstrip even the best of current non-quantum supercomputers. While their efforts have mostly been directed towards science and research rather than security and military objectives, the fundamental processes of quantum computation could reasonably be applied to such goals.

Limits and the Future
For now, quantum computers are highly sensitive and unreliable in everyday conditions: heat, electromagnetic fields, and moving air molecules can change the quantum states of the qubits in unpredictable ways. Google’s report on their latest quantum computing advancements cites the need for further engineering to limit these errors in order to fully realize the abilities of quantum computers. It is important to emphasize that most of the projected consequences of quantum technology are based on its potential, rather than its present capabilities. However, at the current pace of advancement and the rapid increase in public and private investment into quantum technology, we should be prepared to grapple with the threats and opportunities posed by the coming quantum revolution.
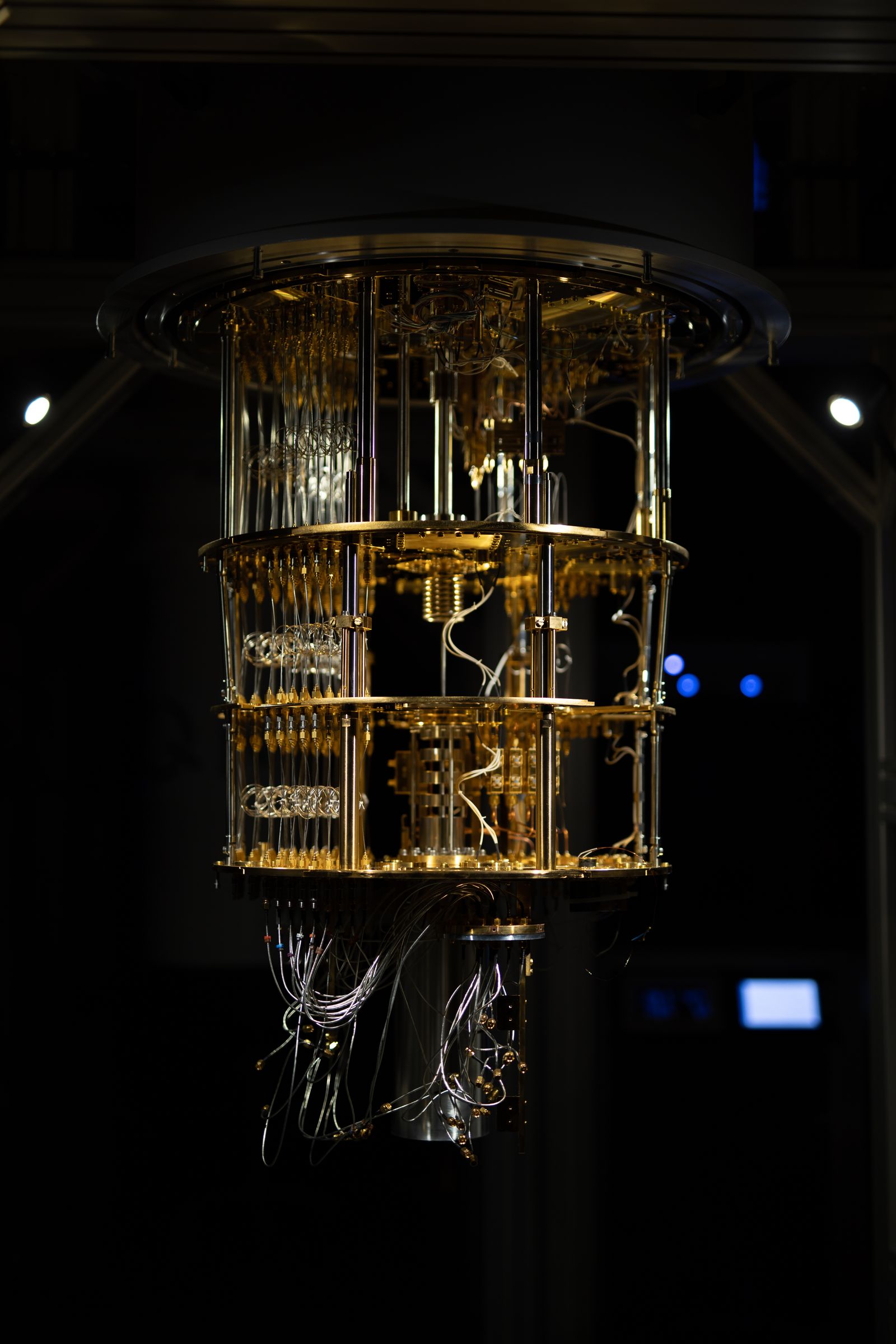
Cover photo: Picture of a working IQM quantum computer installed in Espoo, Finland. IQM is the European leader in building superconducting quantum computers. Photo by Ragsxl, licensed under CC BY-SA 4.0, via Wikimedia Commons.